Posted by Virus Bulletin on Jan 31, 2014
Macros disabled in modern versions of Office, but enabled within many organisations.
A report by the National Cyber Security Center (NCSC, the Dutch CERT) points to a resurgence of macro viruses in targeted attacks.
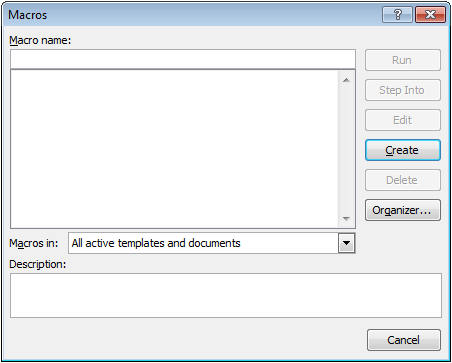
Macro viruses are viruses that are written in a software's built-in macro language. They were very common in the late 1990s, and usually exploited the ability of Microsoft Office to store commonly executed patterns in macros. Macros can be called by certain key-strokes or mouse-clicks, but also automatically - for instance when a document is opened.
In modern versions of Office, the ability to record and execute macros is disabled by default, and thus macro viruses have ceased to be a problem for most home users. However, the NCSC notes that many organisations have macros enabled - for instance to support corporate house styles.
This situation is being abused by some advanced persistent threats: many APT attacks start with someone at the targeted organisation receiving an email with a malicious document attached to it. The NCSC reports that in some cases, macros in these attachments are being used to download malware onto the target's system.
The NCSC notes that these attacks are very targeted and thus the term 'macro virus' might be slightly inappropriate. Moreover, a hesitance among victims to report the attacks and low detection by anti-virus software means it is hard to get an accurate picture of how prevalent they are.
The report, which so far has only been published in Dutch, can be downloaded here.
Posted on 31 January 2014 by Martijn Grooten