Posted by Virus Bulletin on Oct 21, 2011
Landing page contains clear warning.
A phishing email targeting Austrian credit card users evades web filters by using an attached HTML form, but thankfully the landing page on the real website has a clear warning.
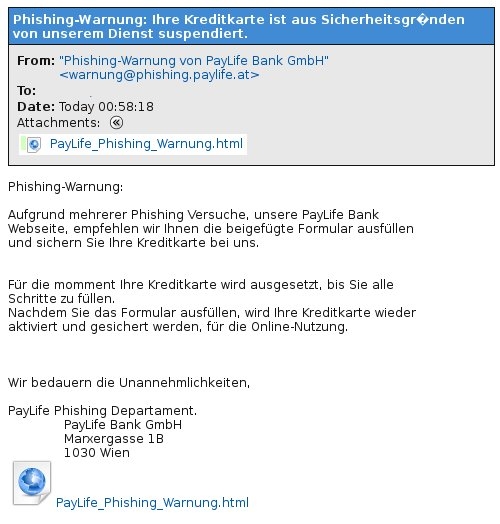
The email, written in far from fluent German, claims to be sent from PayLife, Austria's largest facilitator of financial transactions. It warns the user their credit card has been blocked, ironically because of 'various phishing attempts', and urges them to fill in the form attached to the email to re-activate their card.
The use of an HTML document attached to a spam message, rather than a link to a (fake) website, is not a new technique; spammers use it to avoid web filters. It puts all the burden the spam filter and thus we found it slightly worrying that more than half of the filters participating in the VBSpam tests missed this email.
The form submits a HTTP POST request to a PHP file on the domain egurman dot com dot ua. This appears to be a legitimate if inactive Ukrainian website, which has likely been hacked. The PHP document no doubt sends the credit card information to the phishers before seamlessly redirecting the user to the real PayLife website.
However, we were pleased to notice that PayLife has put a clear message on the landing page: it warns the user that if they just filled in a form, they have been phished and should contact PayLife by phone immediately.
We have notified the owner of the Ukrainian domain.